In today's digital world, cybersecurity is paramount. Individuals of all scales are increasingly exposed to dangerous cyberattacks. This is where white hat hacking comes into play as a vital protective measure. Ethical hackers proactively identify vulnerabilities in systems before malicious actors can, effectively acting as your cybersecurity shield.
- Using simulated attacks, ethical hackers provide valuable insights into the weaknesses of your systems.
- They then suggest remediation strategies to mitigate these vulnerabilities, strengthening your overall cybersecurity posture.
By investing in Hire a hacker ethical hacking services, you can proactively defend your valuable data and avoid the danger of a harmful cyberattack.
Demand a Hacker? Ethical Solutions For Your Digital Fortress
In today's dynamic digital landscape, protecting your data is paramount. But what happens when you suspect a vulnerability? Do you despair? Absolutely not! Instead, consider the powerof ethical hacking. This isn't about malicious intrusions; it's about proactively pinpointing weaknesses in your systems before malicious actors can exploit them. Ethical hackers act as your digital bodyguards, meticulously assessing your networks and applications to bolster your defenses. By embracing ethical hacking practices, you can transform potential threats into opportunities for growth and improved security.
Navigating the Murky Waters of Hackers for Hire
In today's digital age, the line between ethical hacking and malicious cyber activity has become increasingly blurred. Freelance security experts offer their skills to individuals and organizations alike, but navigating the legal and ethical implications of such engagements can be a perilous undertaking. While some hackers operate within established boundaries, others exploit vulnerabilities for personal profit.
Organizations must carefully vet potential consultants to mitigate the risk of unknowingly partnering with individuals who operate outside legal and ethical norms. Moreover, it is crucial to establish clear objectives and limitations at the outset of any engagement with a hacker for hire. Failure to do so can result in unintended repercussions.
- Transparency is paramount in this realm, as both parties should be cognizant of the potential legal and ethical ramifications involved.
- Thorough investigation is essential to ensuring that any partnership with a hacker for hire adheres to all applicable laws and regulations.
Safeguarding Your Digital Assets from Cyber Threats
In today's online world, our financial information is constantly at risk from nefarious attacks. Cybersecurity experts are committed to assisting individuals and organizations in preserving their valuable data from these ever-evolving threats. A competent cybersecurity expert can deploy a robust security framework to reduce the risk of cyberattacks.
- Installing security updates promptly helps prevent known vulnerabilities from being exploited by attackers.
- Avoid using the same password for multiple accounts.
- Be cautious of suspicious emails and links, as they may lead to phishing scams or malware infections.
By following these tips and collaborating with a cybersecurity expert, you can significantly enhance your online security and protect your valuable data from malicious attacks.
Discovering Hidden Risks in Your Systems
In the ever-evolving landscape of cyber threats, organizations need to prioritize their protection. Penetration testing, also known as ethical hacking, provides a proactive approach to identify vulnerabilities before they are exploited by malicious actors. By simulating real-world attacks, penetration testers can uncover weaknesses in digital assets and operational processes. This methodology involves a series of controlled tests that replicate the actions of malicious hackers.
Via these simulated attacks, penetration testers uncover potential vulnerabilities, allowing organizations to address them before they can be exploited by cybercriminals. Effective penetration testing offers invaluable safeguards against a wide range of threats, including data breaches, service disruptions, and financial losses.
Building a Cyber-Resilient Future with Ethical Hacking Strategies
In today's interconnected world, safeguarding our cyber realms from malicious threats is paramount. Building a robust cyber-resilient future requires a multifaceted approach, and ethical hacking stands out as a effective tool in this endeavor. By replicating real-world attacks, ethical hackers help organizations identify weaknesses in their systems before they can be exploited by malicious actors.
Through penetration testing, ethical hackers intentionally probe for security gaps, providing valuable insights into the organization's security architecture. This knowledge empowers organizations to strengthen their defenses, implement appropriate safeguards, and ultimately build a more secure digital environment.
- Ethical hacking plays a significant role in fostering a culture of security within organizations.
- Ongoing ethical hacking assessments help identify and address emerging threats.
- By partnering with ethical hackers, organizations can gain valuable expertise and best practices.
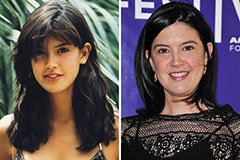 Phoebe Cates Then & Now!
Phoebe Cates Then & Now! Tina Majorino Then & Now!
Tina Majorino Then & Now! Batista Then & Now!
Batista Then & Now! Jeri Ryan Then & Now!
Jeri Ryan Then & Now! Naomi Grossman Then & Now!
Naomi Grossman Then & Now!